Table of Contents:
Author: Ofer Rosenbloom
Executive Summary: The High Cost of Reactive Security
In the modern enterprise, cybersecurity is no longer viewed as a purely technical function—it is a fundamental pillar of financial stability, legal defense, and corporate governance. Today's threat landscape is defined by speed, scale, and severe operational disruption. For C-level executives and Risk Managers, the prevailing reality is that relying on a "reactive" security posture carries significant risk. Attempting to navigate the complexities of a cyber security incident without a pre-established partnership often introduces critical administrative and operational delays, and in the realm of cybersecurity, any hesitation can exponentially increase financial and reputational damages.
The most effective mechanism to mitigate this risk is having a professional Incident Response (IR) team on call. A pre-established IR partnership acts as a proactive financial, legal, and operational safeguard. By establishing predefined Service Level Agreements (SLAs), pre-negotiated rates, and a deep familiarity with your business landscape and network architecture before an attack ever happens, an on-call IR team transforms chaotic crisis management into a controlled, predictable process. At HackersEye, our elite on-call IR services are engineered to deliver a demonstrable Return on Investment (ROI), ensuring your enterprise is fully armed and ready the moment a crisis strikes.
The Economics of Incident Response (Financial ROI)
For the C-suite and senior business leaders, cybersecurity investments must be justified by hard data and strategic value. The economics of a pre-established IR partnership are undeniable when compared to the staggering costs of a data breach.
Mitigating the Multi-Million Dollar Breach: According to the 2025 IBM Cost of a Data Breach report, the global average cost of a breach stands at $4.44 million, while in the United States, it has surged to an unprecedented $10.22 million. However, IBM data clearly proves the financial value of established, rapid-response capabilities: when an organization's own security apparatus identifies and contains the breach first, the average cost drops to $4.18 million, compared to a devastating $5.08 million when the breach is disclosed by the attacker. Having an expert team on call ensures immediate mobilization, directly contributing to this significant cost reduction.

Bar chart comparing the financial impact of a data breach based on how it is identified. A breach identified by internal security teams costs an average of $4.18 million, while a breach disclosed by an attacker costs an average of $5.08 million. Data sourced from the 2025 IBM Cost of a Data Breach Report.
The Hidden "Total Cost of Recovery": The initial ransom demand, downtime or data loss are rarely the final financial blow. Data from the Sophos State of Ransomware 2025 report indicates that while the average ransom payment is $1.0 million, the average overall recovery cost actually eclipses the ransom itself, reaching $1.5 million. This proves that organizations cannot simply pay their way out of a crisis; they require elite forensic intervention to rebuild and recover.
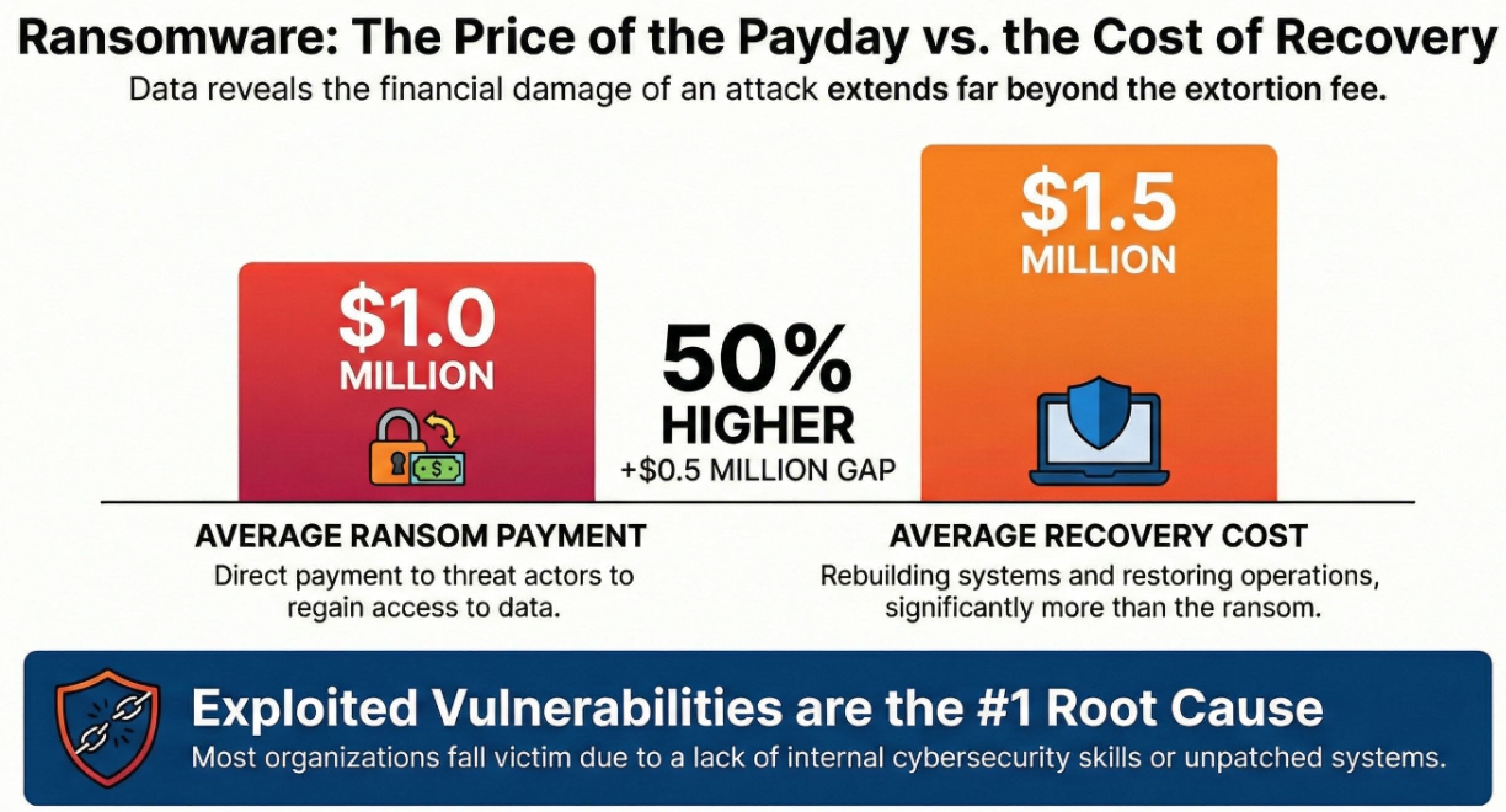
Data visualization showing the hidden costs of a ransomware attack. The average ransom payment is $1.0 million, but the average recovery and remediation cost is much higher at $1.5 million. Data sourced from the Sophos State of Ransomware 2025 report.
Minimizing Business Interruption (BI): The most devastating financial impact of a cyber incident is downtime. Data from NetDiligence reveals that the 5-year average for Business Interruption (BI) costs is $1.8 million for Small to Medium Enterprises (SMEs) and a staggering $26.0 million for large companies. An on-call IR team eliminates administrative delays, dramatically minimizing the operational downtime that drives these massive BI losses.
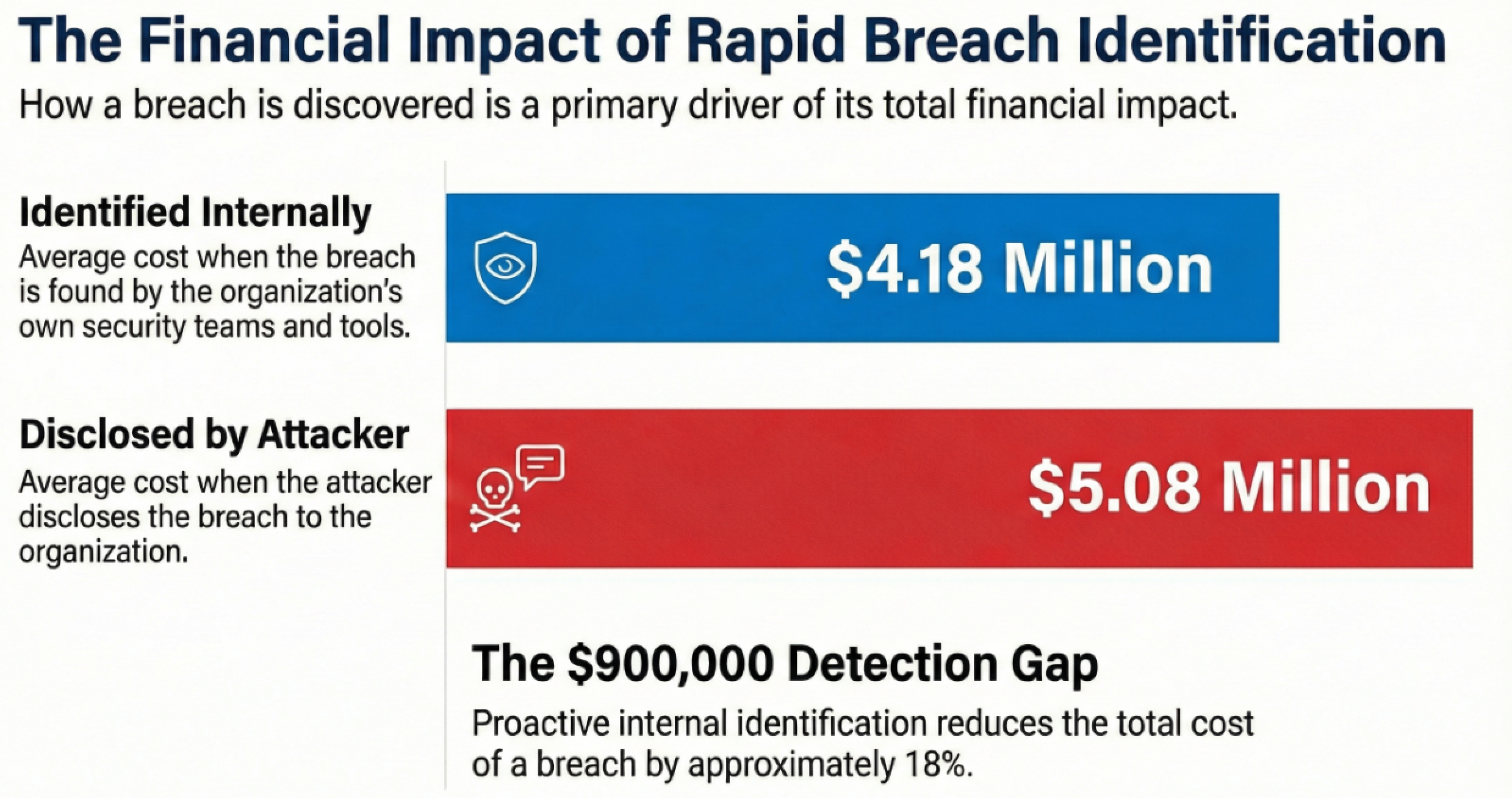
Chart detailing the average total cyber incident costs segmented by organization size. Small to Medium Enterprises under $2 billion in revenue face an average incident cost of $264,000, whereas large companies over $2 billion in revenue face an average cost of $10.3 million. Data sourced from the NetDiligence Cyber Claims Study 2025.
Technical & Operational Superiority
Internal IT teams are built to maintain business continuity and manage infrastructure; they are rarely equipped to conduct the highly specialized digital forensics required during a sophisticated nation-state or ransomware attack. Relying solely on internal resources during a critical incident often leads to compromised evidence, extended downtime, and worst of all, re-infection.
Slashing Dwell Time and MTTD/MTTR: The longer an attacker remains in your environment, the more data they exfiltrate. Elite on-call IR teams drastically compress this timeline. IBM data notes that the global mean time to identify and contain a breach currently sits at an average of 241 days, but having proactive security capabilities and expert resources on hand significantly accelerates detection and containment, minimizing the window of opportunity for threat actors.
Preventing Re-Infection: A common pitfall for internal IT teams is restoring systems from backups before fully understanding the root cause of the intrusion. Threat actors frequently utilize multiple persistence mechanisms, such as hidden backdoors, meaning that systems are easily re-infected if eradication is not exhaustive. An on-call partnership with HackersEye brings the specialized digital forensics and incident response (DFIR) expertise required to analyze complex adversary tactics, techniques, and procedures (TTPs), ensuring total eradication and preventing the attacker from utilizing alternative attack vectors to regain access.
Navigating the Legal, Regulatory & Insurance Labyrinth
For General Counsels and Risk Managers, a cyber incident is simultaneously a legal and regulatory crisis. How an incident is investigated and reported directly dictates the organization's exposure to class-action lawsuits, regulatory fines, and denied insurance claims.
Protecting Legal Privilege and Mitigating Lawsuits: Post-breach litigation is a rapidly growing threat. BakerHostetler's 2025 Data Security Incident Response Report notes that 51 disclosed incidents in their dataset resulted in one or more class-action lawsuits. Engaging an IR team through outside counsel helps protect the forensic investigation under attorney-client privilege. This limits legal exposure and provides a structured, defensible narrative to regulators and shareholders.
Reducing Regulatory Fines: Mishandling an investigation can lead to significant regulatory penalties, as seen in multimillion-dollar settlements across various industries. Prompt, accurate forensic reporting from a retained expert ensures compliance with stringent disclosure timelines, directly mitigating regulatory fallout.
Maximizing Cyber Insurance Benefits: The cyber insurance market has hardened, and carriers now demand proof of proactive readiness. Insurance carriers heavily favor organizations that have pre-vetted, elite IR firms on call. Establishing this relationship not only satisfies carrier readiness requirements but can also be leveraged to negotiate better policy premiums and lower deductibles, effectively offsetting the cost of the service.
The Strategic Advantage of Repurposing Hours
The most common objection from business leaders regarding on-call security contracts is: "What if we don't get breached? Are we just paying for a service we might not use?"
Security budgets must deliver continuous value. Leading on-call IR partnerships, such as the model we employ at HackersEye, extend far beyond emergency response by integrating continuous proactive defense mechanisms. We guarantee a positive ROI regardless of whether a major incident occurs by actively monitoring your environment and neutralizing threats before they weaponize.
At HackersEye, your on-call partnership continuously delivers value through:
- Attack Surface Management (ASM): The speed of modern cyberattacks requires constant vigilance. According to the Unit 42 Incident Response Report, attackers typically begin scanning for vulnerable systems within just 15 minutes of a new CVE (Common Vulnerabilities and Exposures) being announced. HackersEye provides continuous attack surface management to identify vulnerable or exposed systems and catch rogue assets that organizations may not even be aware are running on their network.
- Real-Time Threat Intelligence & Asset Monitoring: Relying solely on internal baselines is no longer sufficient. By actively monitoring your critical assets and integrating elite cyber threat intelligence (CTI), our team identifies widespread scanning efforts and blocks known malicious behavior and adversary TTPs early in the attack lifecycle.
- Measurable Cost Reduction: This proactive approach has a direct, mathematical impact on the bottom line. Data from the 2025 IBM Cost of a Data Breach Report reveals that deploying proactive threat hunting and attack surface management tools reduces the average cost of a data breach by $193,242 and $160,547 respectively per incident.
Conclusion: A Pillar of Corporate Governance
In today's digital economy, having a dedicated Incident Response team on call is not merely a technical luxury; it is a measurable financial asset and a core pillar of corporate governance. Attempting to navigate the complexities of a modern cyberattack without a pre-established partner results in operational paralysis, catastrophic business interruption, and severe legal liability.
By establishing a proactive relationship with HackersEye, organizations secure the immediate backing of elite digital forensic experts, satisfy stringent cyber insurance requirements, and gain a proactive ally dedicated to monitoring critical assets and managing the attack surface every single day.
Do not wait until the network goes dark and operations grind to a halt. Establish your on-call IR team today and secure the resilience your enterprise demands.


